Track. Verify. Protect.
The first-of-its-kind AI-powered platform to detect, monitor and prevent unauthorized moonlighting with precision. It uncovers undisclosed secondary employment, conflicts of interest and productivity risks before they escalate into compliance failures or public incidents.
4.1 On 
3.8 On
3.7 On
Trusted by 10,000+ businesses worldwide
Moonlighting is a Risk-and an Opportunity
Unmanaged side jobs can drain productivity, leak intellectual property and trigger policy or contractual breaches. We turn that risk into an opportunity to protect revenue, culture and compliance.
Employees should know: undisclosed secondary employment leaves a trail. Companies can act early-fairly, lawfully and with evidence.
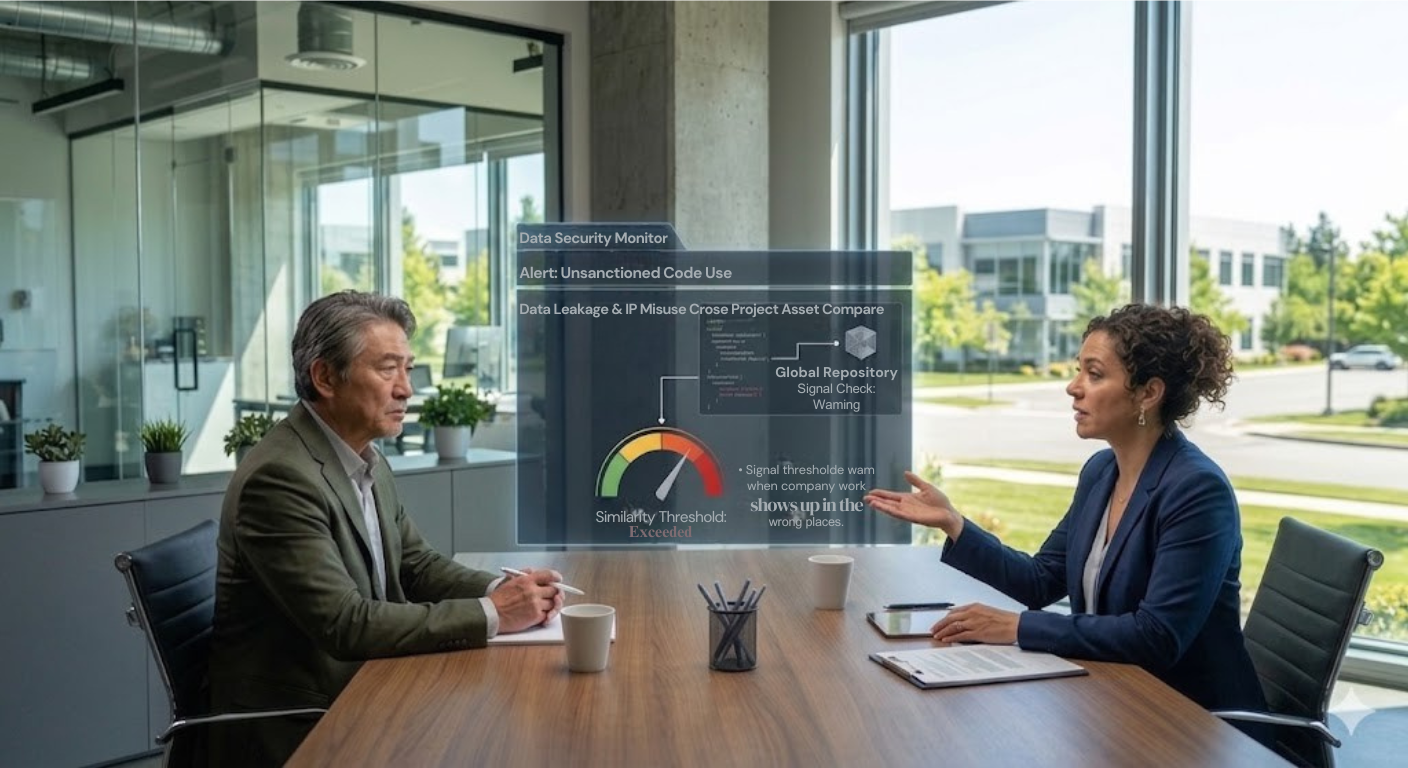
IP Leakage Prevention
Conflict of Interest Signals
Productivity & Burnout Risk
Compliance & Audit Ready


Why Monitoring
Moonlighters Matters
Customer stories
Loved by teams of all sizes
ManyQuest helped us quickly identify employees associated with multiple organizations. It significantly improved our internal compliance checks and hiring verification process.
The platform gives us clear visibility into employee affiliations across companies. ManyQuest has become a valuable tool for risk detection and workforce transparency.
ManyQuest makes it easy to identify potential risk employees who are working with multiple companies simultaneously. This insight helps us maintain stronger compliance standards
With ManyQuest, we can detect overlapping employment records in seconds. It’s a powerful solution for organizations that prioritize transparency and accountability.
ManyQuest helped our recruitment team verify employee background data quickly and accurately more efficiently. It adds an extra layer of trust to our hiring process.
The risk employee detection feature of ManyQuest is incredibly useful. It helps businesses identify potential conflicts of interest quickly.
ManyQuest provides clear insights into employee associations across organizations. This level of visibility helps companies manage workforce risks effectively.
Tracking employee affiliations across companies used to be difficult. ManyQuest simplified the process and gave us accurate and reliable data in one place.
ManyQuest delivers valuable insights into employee activity across multiple companies. It helps us detect and resolve compliance issues early.
The platform helps organizations ensure employees follow company policies regarding external employment. ManyQuest adds transparency to workforce management.
ManyQuest provides the clarity companies need when verifying employee associations. It’s a reliable and efficient platform for managing workforce risks.
As a growing company, ManyQuest helps us quickly identify potential employee conflicts across organizations and take corrective action when needed.
Signals Built for Detection
Precise, explainable signals that turn suspicion into evidence and risk into action-without invasive monitoring.
Anomaly & Pattern Alerts
After‑hours spikes, parallel client footprints and code reuse signals-delivered as clear, configurable alerts.
- Early intervention windows
- Thresholds fit to policy & role
- Noise‑reduced signal scoring
Risk Trends Dashboard
Track risk by team, location and role. See how policy changes reduce moonlighting pressure over time.
- Visual trend analysis
- Hotspot and cohort views
- Outcome‑based KPIs
Case Builder & Evidence
Export defensible, time‑stamped evidence packs for HR and Legal-mapped to your policy clauses.
- Policy clause mapping
- Audit‑ready timelines
- Secure share links

Ready to See Who’s Working in the Shadows?
For employees: undisclosed side gigs risk contracts and careers. For companies: clarity protects culture, clients and IP.
Start Your Risk ReductionHow Our Solutions Work Together
A single unified platform that transforms fragmented workforce signals into powerful organizational intelligence.
Data Aggregation
Securely collect workforce data from HR platforms, productivity tools, and internal systems.
AI Analysis
Advanced pattern recognition and anomaly detection using privacy-preserving algorithms.
Insights Generation
Convert analyzed data into clear, actionable intelligence tailored for different stakeholders.
Protected Delivery
Role-based access ensures the right insights reach the right decision-makers securely.
Unified Intelligence Dashboard
All four solution pillars combine into a single intelligent dashboard that provides a complete view of workforce health and enables proactive decision-making.